IT Consulting Leicester: Risk-Driven, Audit-Ready Technology for SMEs
Secure, scalable technology for SMEs and IT managers—cloud, cybersecurity, Microsoft 365, helpdesk and web performance—backed by UK standards and measurable KPIs to cut risk, control spend and accelerate growth.




Unpatched devices, expanding SaaS, remote users, and websites missing Core Web Vitals create outages, higher breach risk and poor conversion. Boards are now expected to treat cyber as a business risk, with clear accountability and evidence.
Why Leicester SMEs Face Rising Cyber & Web Performance Challenges
Are IT Gaps Putting Your Business at Risk? Key Warning Signs
- Growing ticket backlog, slow Wi-Fi/VPN, messy identity & access, shadow IT
- No MFA/conditional access; weak email security; backups untested (unclear RPO/RTO).
- Inconsistent cookie consent and data minimisation against PECR/GDPR.
- Websites failing LCP/INP/CLS thresholds (especially mobile), harming search and sales.
Get Security, Speed & ROI—All Measured by Real KPIs
- Stability & speed: incident rate and MTTR trend down; structured change windows.
- Security posture: MFA by default, baseline-hardened endpoints, phishing failure rate reduced, Cyber Essentials journey planned and evidenced.
- Cloud clarity: Microsoft 365 governance (Entra ID/Intune), rightsized licenses, retention and access reviews (least privilege).
- Measurable web performance: CWV targets met (LCP ≤2.5s, INP ≤200ms, CLS ≤0.1) with diagnostics and fixes
- Audit-ready operations: logs, tabletop exercises, policies and consent records that satisfy auditors and boards.
See Your Progress: From Reduced Incidents to Faster Websites
| Objective | KPI | Indicative Range | Evidence Cadence |
|---|---|---|---|
| Reduce downtime | MTTR | 30–60% improvement | Monthly ops report |
| Improve security | Patch compliance | ≥95% within 7 days | Patch dashboard |
| Harder to phish | Phishing failure rate | ↓ over 2–3 campaigns | Security report |
| Boost UX/SEO | LCP/INP/CLS | ≤2.5s / ≤200ms / ≤0.1 | CWV dashboard (web.dev) |
| Cost control | Cloud/SaaS spend | −10–25% wastage | Quarterly review |
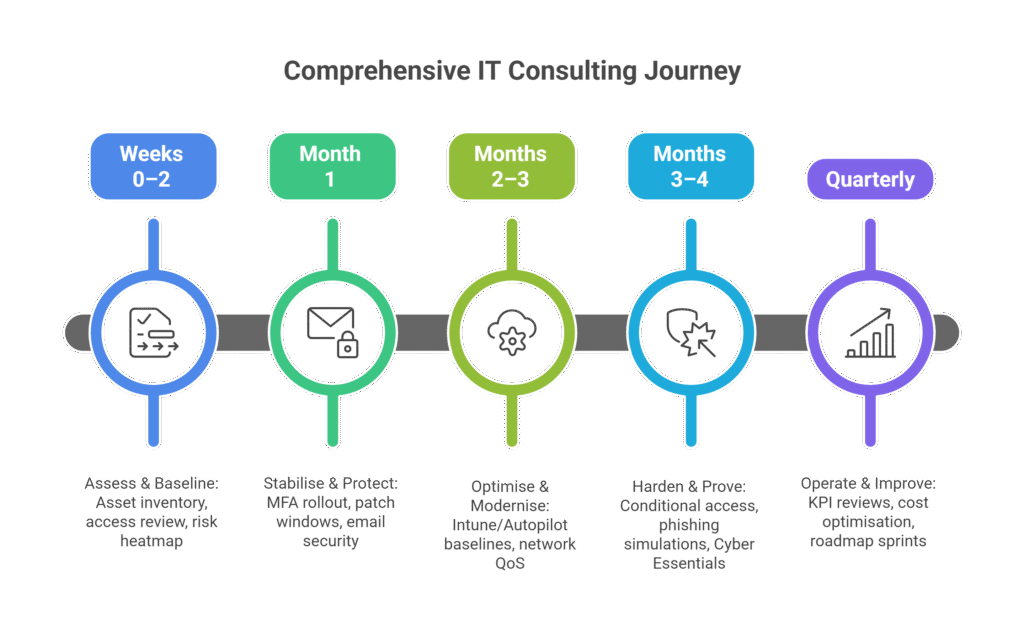
Our IT Consulting Process: Assess, Secure, Optimize & Prove
Assess & Baseline (Weeks 0–2)
Asset inventory, access review, risk heatmap and maturity benchmark mapped to NCSC Board Toolkit and Cyber Governance Code
Stabilise & Protect (Month 1)
MFA rollout; patch windows; email security & DLP; backup & restore test (define RPO/RTO); cookie consent with ICO-compliant UX.
Optimise & Modernise (Months 2–3)
Intune/Autopilot baselines, network QoS, rightsizing Microsoft 365; CWV remediation (critical CSS, image policy, script defers).
Harden & Prove (Months 3–4)
Conditional access, privileged access workflows, phishing simulations, tabletop IR exercise; Cyber Essentials evidence pack.
Operate & Improve (Quarterly)
KPI reviews, cost optimisation, accessibility checks, change governance, roadmap sprints.
What Does IT Consulting Cost? Leicester SME Pricing & Value
Projects
audits, migrations, network refresh, incident-readiness, CE/CE+ remediation (scoped, fixed deliverables).
Managed Service (MSP/MSSP)
helpdesk, patch/EDR, identity & access, backup/DR tests, phishing sims, reporting (per-user/device retainer).
IR Retainer (optional)
on-call response hours, tabletop cadence, evidence & comms templates.
ROI framing
fewer incidents (time saved), less cloud wastage, improved CWV → better conversion (documented with benchmarks).
UK Cyber & Data Compliance Made Simple—From GDPR to Cyber Essentials
GDPR/PECR
lawful basis & DPIAs; consent for non-essential cookies; retention & deletion; minimise tracking.
Cyber Essentials / Plus
five controls, assessment route, CE+ technical audit; evidence-ready runbook
Board accountability
align with the Cyber Governance Code and use the NCSC Board Toolkit for ongoing oversight.
Sector cues
NHS (DSPT), FCA (operational resilience) [NEEDS VERIFY]; telecom/VoIP integrations aware of Ofcom rules (e.g., CLI presentation updates).
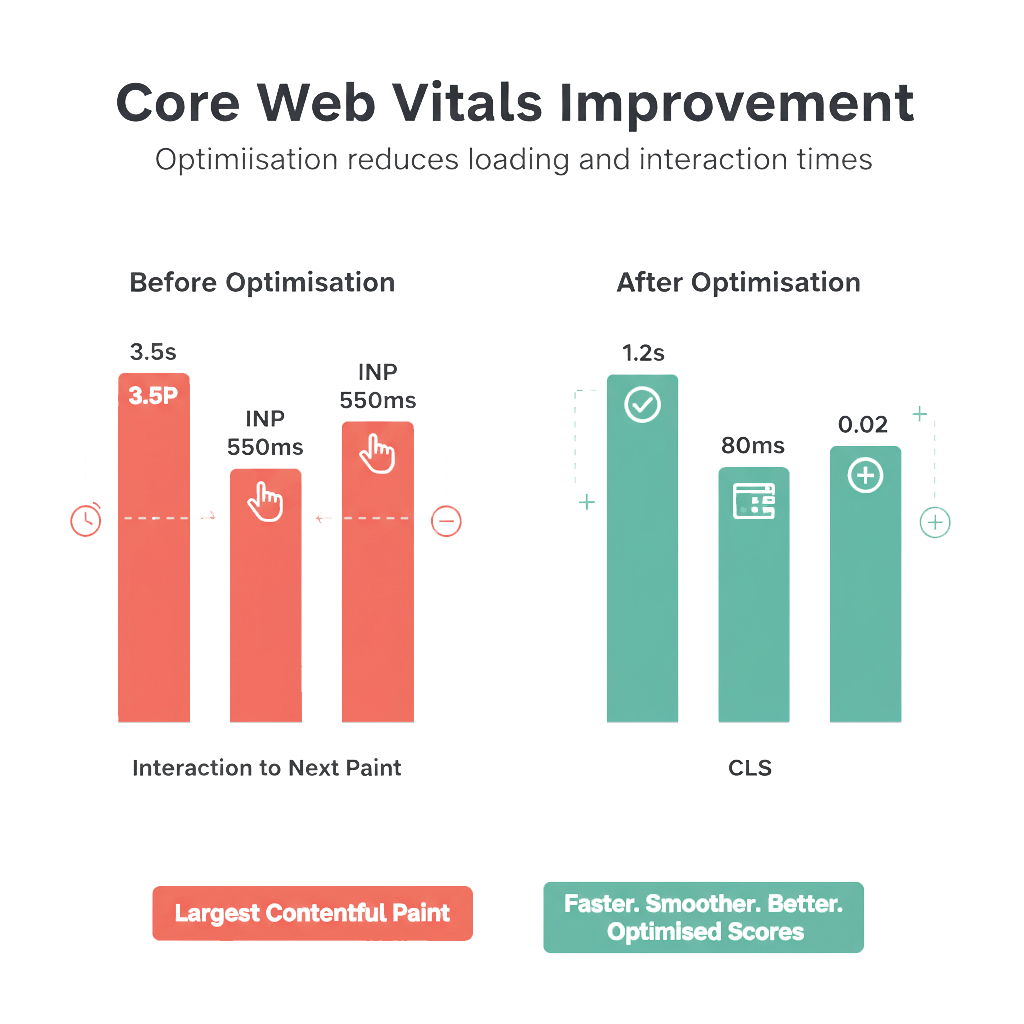
Page Speed & SEO for IT Services—How We Meet Core Web Vitals
Architecture & Indexation
One canonical per template; clean XML sitemaps; robots.txt blocks only staging; fix crawl traps; maintain internal pillar→spoke links.
Page Speed & INP/LCP/CLS Targets
LCP ≤ 2.5s, INP ≤ 200ms, CLS ≤ 0.1 (mobile). Prioritise image policy, critical CSS, early hints, defer non-critical JS, edge cache HTML for anon users.
JavaScript SEO
Prefer SSR/prerender for primary content; lazy-hydrate widgets; code-split vendor bundles; keep TTFB low via CDN edge + caching.
Core Web Vitals Box
| Metric | Target | Typical Fixes |
|---|---|---|
| LCP | ≤2.5s | Preload hero image/font; compress; reduce render-blocking CSS/JS. (web.dev) |
| INP | ≤200ms | Break long tasks; input profiling; defer third-party JS. (web.dev) |
| CLS | ≤0.1 | Reserve space; font-display swap; stabilise ads/embeds. (web.dev) |
Authority-Building IT Content & Internal Linking
Topic Clusters & Internal Linking
Pillar (IT Consulting Leicester) → spokes: /it-support, /cyber-security, /policies, /case-studies, /resources. Each spoke links back to pillar + sibling spokes to distribute authority.
Schema & Rich Results
Implement ProfessionalService/Service, FAQPage, Organization/LocalBusiness, BreadcrumbList; tools = SoftwareApplication when applicable.
Reviews & Social Proof
Collect first-party reviews; be CAP-Code sensible; surface AggregateRating only when policy allows; don’t set tracking cookies without PECR consent.
Conversion-Optimized WordPress Sites for IT Leaders
UX Patterns
- Off-site backups + restore drills
- Proof bar (Cyber Essentials journey, partner badges).
- Comparison modules (in-house vs MSP/MSSP; MDR vs SIEM-only).
Accessibility (WCAG 2.2) Quick-Wins (checklist)
CRO Tactics
Sticky CTAs; short forms (name, email, company, 1 goal); reassurance copy; WhatsApp/phone fallback; place social proof right beside the form.
Reliable Hosting: Fast, Secure and Monitored for IT Consulting
Uptime/SLA & Monitoring
Aim ≥99.9% uptime; synthetic + RUM; incident timeline and post-mortems tied to the cyber governance workstream.
Edge/CDN & Caching
Edge cache HTML (anon); far-future TTL with versioning on assets; vary cache keys by auth; monitor TTFB as a lead indicator for CWV.
Backups, Security Hardening & Updates
Daily off-site backups, quarterly restore tests; WAF/CDN; MFA for hosting/CMS; least-privilege accounts; staging with rollback plan (blue/green where possible).
Hosting/SRE Readiness Checklist
☑ Off-site backups + tested restores (RPO/RTO) · ☑ WAF/MFA · ☑ Staging + rollback · ☑ Uptime alerts · ☑ Access reviews · ☑ Patch windows.
Real-World Results: How Leicester Firms Levelled Up Security & Speed
Phishing controls
After two simulation rounds and training refresh, failure rate trends downward; execs get board-readable report mapped to the Board Toolkit.
Cyber Essentials journey
Scope, remediate, evidence; optional CE+ technical audit prepared.
CWV uplift
Your 30/60/90-Day IT Transformation Roadmap
Days 0–30:
Baseline + MFA; backup/restore test; cookie consent & DPIA; quick CWV wins.
Days 31–60
Intune baselines; network QoS; license rightsizing; first phishing campaign.
Days 61–90
CE evidence pack; tabletop IR; accessibility audit; KPI review; roadmap sprint.
IT Consulting Leicester: Frequently Asked Questions
Consulting sets the strategy and designs change; managed support runs daily ops (helpdesk, patch, monitor). Many Leicester firms choose a co-managed blend.
CE is self-assessment; CE+ adds an independent technical audit for assurance that controls are in place.
Yes, for most non-essential cookies under PECR; obtain explicit consent and document it.
LCP ≤2.5s, INP ≤200ms, CLS ≤0.1 (mobile, 75th percentile).
Yes—clear RACI, shared dashboards, and change windows.
Yes—Entra ID, Intune baselines, conditional access, DLP and mailbox security aligned with UK guidance.
Trend MTTR and ticket volume, patch compliance, phishing results, CWV field data, and cloud cost reports.
For voice/Teams integrations we follow provider guidance and keep an eye on Ofcom updates (e.g., CLI presentation rules).
Runbook, tabletop exercise, priority contacts, comms templates, and optional IR retainer.
No—WCAG 2.2 quick wins are lightweight and usually improve UX and conversions.
Try Our Free Risk Tools
Risk Scoring Mini-Tool
answer 10 controls → maturity band + next 3 actions.
Backup RPO/RTO Calculator
enter data change rate & tolerance → recommends frequency + test cadence.
Breach-Cost Estimator
records at risk × likelihood × unit impact → order-of-magnitude planning (board-friendly).
TTFB/CWV Check
test key pages; if TTFB >400 ms or LCP >2.5 s, apply caching & image fixes.
Explore Our IT Consulting Services in Leicester
Managed IT Support
Flexible managed IT support plans
Cyber Security Services
Proactive cyber security & Managed Detection and Response (MDR
Latest Resources
Downloadable guides, checklists & industry templates
Client Testimonials
Hear from businesses we’ve helped across Leicestershire
Whether you’re a growing SME or an established organisation, our expert team delivers tailored technology solutions designed to keep your business secure, compliant, and efficient.
All services are locally delivered with national standards—serving Leicester, Loughborough, Hinckley, and the wider East Midlands.
Trusted by Industry Authorities & Best Practices
Information Commissioner’s Office (ICO)
Guidance on cookie consent and PECR compliance
GOV.UK: Cyber Essentials
Official details on the Cyber Essentials certification schem
NCSC: Cyber Security Toolkit for Boards
Strategic cyber risk oversight for leadership team
GOV.UK: Cyber Governance Code
Newly launched 2025 Cyber Governance Code of Practice for directors
Google web.dev: Core Web Vitals
Web performance benchmarks for user experience
W3C/WAI: WCAG 2.2 Quick Reference
Accessibility standards for inclusive digital services
We align our consulting approach with the latest UK regulatory guidance and technical standards to ensure your business stays ahead of risk and performance benchmarks.
By integrating these authoritative frameworks, we ensure your IT strategy is resilient, compliant, and future-ready.
What Leicester Clients Say: Google Reviews
See more reviews on our [Google Business Profile], or leave your own experience!
Bhav was friendly, polite and professional. He listened to what we wanted and advised accordingly.We used BhavPro for a Windows 10 Pro to Windows 11 Pro upgrade and secure data migration for our business. Bhav handled the entire process smoothly, with minimal downtime.Our software setup and all client data were fully preserved, and everything worked exactly as before with no disruption to daily operations. Communication was clear and professional throughout, and the work was completed on time. Highly recommend BhavPro for IT support, system upgrades, and secure data handling.
We reached out to BhavPro because we were struggling to figure out the best VoIP setup for our business. They took the time to listen, explained the options in plain English, and recommended a provider that actually fit what we needed (and our budget). The whole process was straightforward, and switching over was way easier than we expected. Call quality is miles better now, and we’ve already saved money compared to our old system. What impressed us most was how BhavPro focused on finding the right solution rather than just selling something. If you’re considering VoIP or telecom consulting, we’d definitely recommend their advice and support. — SR Property Services
Working with BhavPro has honestly been a game changer for us. They didn’t just design a good-looking website — they made sure it was properly SEO-optimized and built to bring in real results. Not long after launching, we started noticing a huge jump in inquiries, and over time it’s grown to nearly 50 times more than before. That consistency has given us the confidence to open another site, which we never thought possible this soon. What we liked most was that BhavPro combined the technical side with genuine business advice. It felt like they cared about our growth as much as we did. We’d happily recommend them to anyone looking for a website that actually delivers and real SEO results. — Almari Designs Ltd
Proudly Supporting Leicester’s SMEs with Risk-Driven IT Consulting
Contact me for a free IT consultation—choose a phone call, video meeting, or in-person session in Leicester.
We can discuss your IT strategy, review your cloud and cybersecurity setup, and map out a practical, governance-first 90-day plan. I’m here to help you cut risk, boost web performance, and ensure measurable results.
Bullet Service Specialties:
IT Consulting, Cloud, Cybersecurity, and Local Business Enablement
Core Web Vitals (LCP/INP/CLS) & Web Performance Diagnostics
Governance-First IT: Cyber Essentials, GDPR/PECR, and Accessibility (WCAG 2.2)
Actionable Reporting and Board-Ready KPIs
📍 Micro-note: Serving Leicester and surrounding areas — Oadby, Wigston, Loughborough, Hinckley, Coalville, and Syston.
Ready to Cut Your IT Risk? Book a Free Consultation Now
Book a free consultation to discuss how we can reduce risk, prove ROI, and align your IT with UK governance standards.